
Anomaly‐based intrusion detection systems: The requirements, methods, measurements, and datasets - Hajj - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library
Proceedings of the 6th International Conference on Communication and Network Security: An Anomaly-based Intrusion Detection Arch

Anomaly network-based intrusion detection system using a reliable hybrid artificial bee colony and AdaBoost algorithms - ScienceDirect
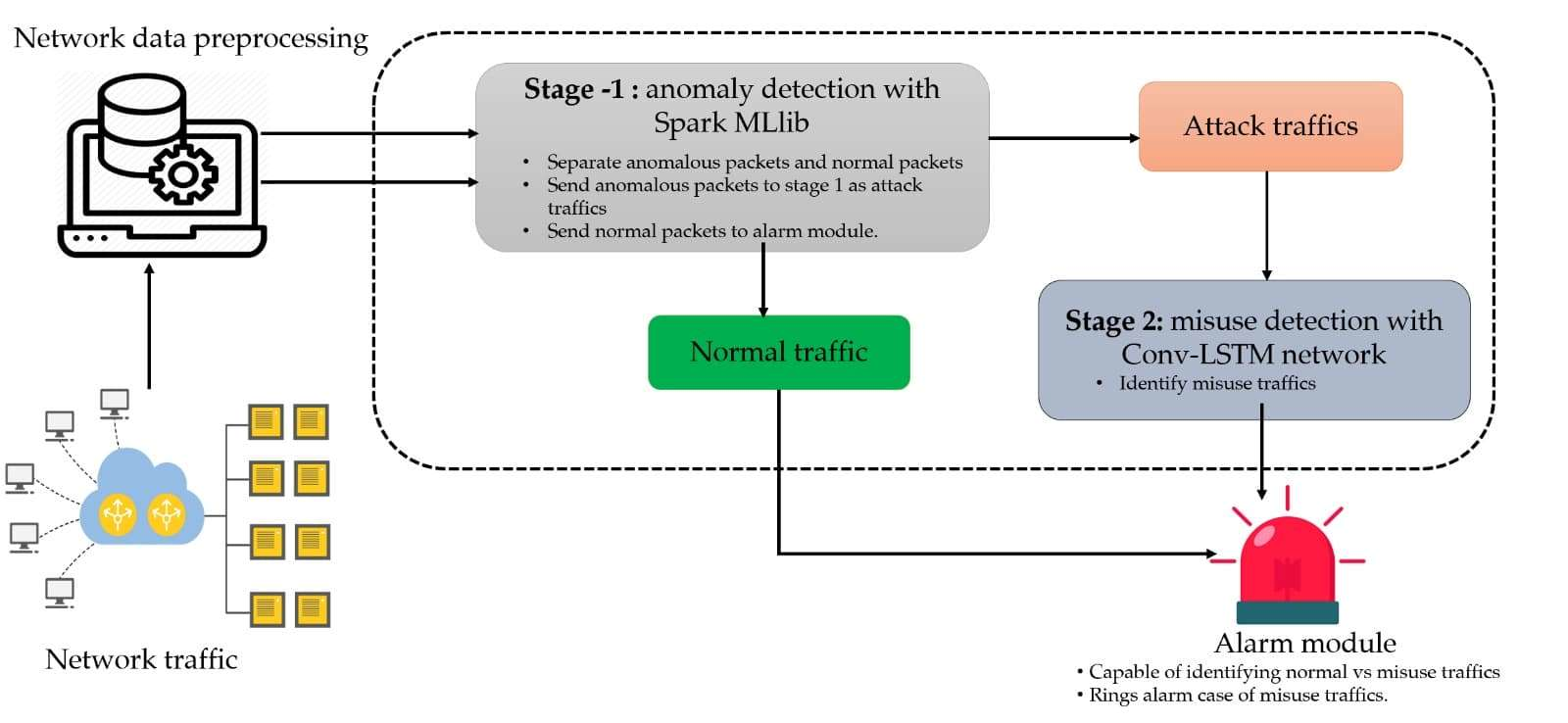
Symmetry | Free Full-Text | A Scalable and Hybrid Intrusion Detection System Based on the Convolutional-LSTM Network
![PDF] Toward a reliable anomaly-based intrusion detection in real-world environments | Semantic Scholar PDF] Toward a reliable anomaly-based intrusion detection in real-world environments | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e0aed1bc82cbe595e723ddc7007aa089e1bb8384/5-Figure2-1.png)
PDF] Toward a reliable anomaly-based intrusion detection in real-world environments | Semantic Scholar

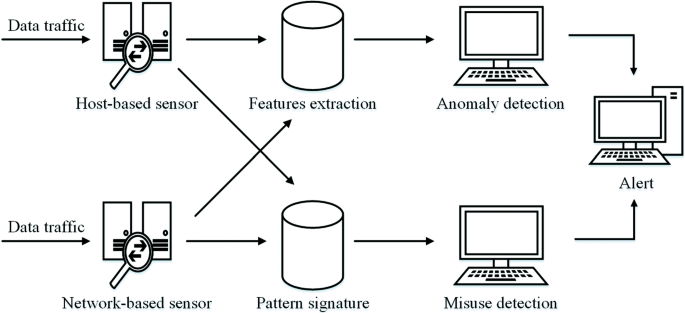
An anomaly-based intrusion detection system (IDS) using datamining to... | Download Scientific Diagram
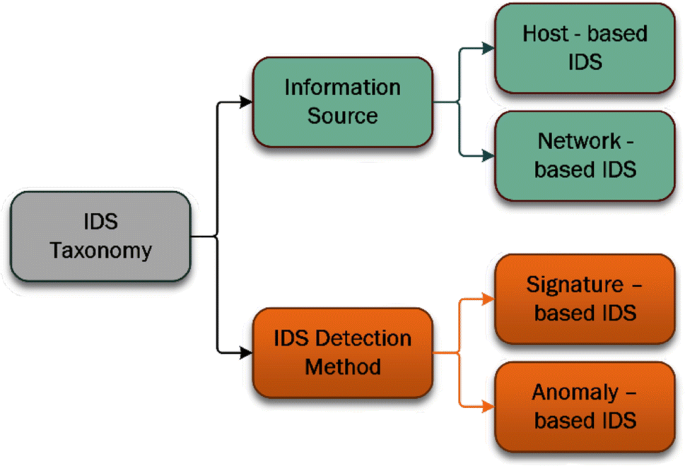
Intrusion detection systems for IoT-based smart environments: a survey | Journal of Cloud Computing | Full Text
Anomaly-based intrusion detection system using multi-objective grey wolf optimisation algorithm | Journal of Ambient Intelligence and Humanized Computing

Anomaly based network intrusion detection for IoT attacks using deep learning technique - ScienceDirect

![PDF] A survey on anomaly and signature based intrusion detection system (IDS) | Semantic Scholar PDF] A survey on anomaly and signature based intrusion detection system (IDS) | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/20ae22409cc115757369fc3d583d4f81d18db164/4-Figure1-1.png)



![SIGNATURE-AND ANOMALY-BASED IDS [5] | Download Scientific Diagram SIGNATURE-AND ANOMALY-BASED IDS [5] | Download Scientific Diagram](https://www.researchgate.net/publication/297171228/figure/fig1/AS:336959961616387@1457348923581/SIGNATURE-AND-ANOMALY-BASED-IDS-5.png)




![PDF] Anomaly-Based Intrusion Detection System | Semantic Scholar PDF] Anomaly-Based Intrusion Detection System | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/9304edc92f60dc5f406340ae7c0cf0180af080bd/5-Figure1-1.png)